The Best MCP Gateway Options for Enterprises
According to a16z, “29% of the Fortune 500 and ~19% of the Global 2000 are paying customers of a leading AI startup.” It’s clear that agents are already operating across engineering, customer support, sales, and operations in enterprise settings. And MCP makes these agents more powerful, filled with the the context and capabilities of external tools.
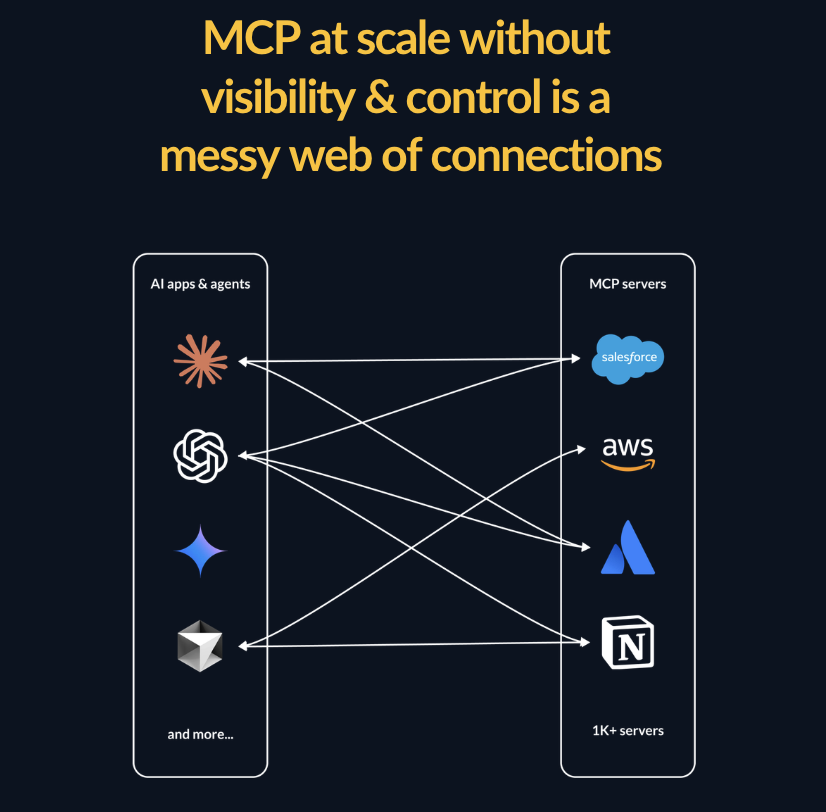
However, without a control layer, every team manages its own agent connections, its own credentials, and its own access logic. This creates exactly the kind of ungoverned sprawl that enterprises spend millions trying to prevent. In fact, Gartner predicts over $1 billion will be spent on AI governance by 2030.
An MCP gateway is the antidote to the exact type of secrets and tool sprawl that enterprises must mitigate to safely roll out AI. By offering a central layer that sits between all of your AI agents and the MCP servers they access, IT teams can get the access and visibility they need to safely roll out MCP-powered agentic workflows.
MCP gateways centralize the following in a single governed layer:
- authentication
- policy enforcement
- PII detection
- approved MCP servers
- observability
- audit logging
- alerts and monitoring
For enterprises, the gateway is what makes the difference between AI agents as a strategic capability and AI agents as an unmanaged risk. This guide covers the best MCP gateway options for enterprise deployments and how to evaluate which one fits your organization.
Why Enterprises Need an MCP Gateway
The case for a gateway sharpens at enterprise scale. More teams, more agents, more tools, more data, more compliance obligations means that there are also exponentially more ways for things to go wrong without centralized oversight. Or, as one Reddit user put it:

MCP Gateways Make Governance at Scale Possible
An enterprise with 20 teams running agents against 50 MCP servers has 1,000 potential connection points.. And each of these connects has its own authentication, access scope, and risk profile. Managing that sprawl through individual agent configurations is operationally impossible without a central control palce.
A gateway bring all these disparate connections into one governed central layer. Agents connect to the gateway; the gateway connects to tools. Add a server once. Enforce a policy once. Rotate a credential once. Audit everything in one place. This is the architectural pattern that makes MCP manageable at enterprise scale.
MCP Gateways Help Enterprises Meet Compliance Requirements
SOC 2, HIPAA, GDPR, PCI DSS, the EU AI Act are some of the most well known compliance requrements that enterprises operate under. Many companies have multiple overlapping compliance frameworks, each requiring demonstrable control over how data is accessed and by whom. AI agents introduce a new dimension to that obligation: every tool call is a data access event that needs to be logged, attributed, and auditable.
A gateway that captures contextual metadata within audit trails, such as time/date, agent identity, tool name, parameters, results, and the human authorization chain, gives compliance teams the evidence they need to regulators without requiring custom instrumentation on every agent.
Gateways Prevent MCP-Specific Security Threats
Prompt injection, tool poisoning, rug pull attacks, and data exfiltration are just some of the attack vectors that are specific to MCP deployments. Traditional API gateways and network security tools weren’t designed to detect or prevent them.
Enterprise MCP deployments need runtime guardrails that understand MCP semantics, such as blocking unsafe operations, detecting abnormal tool-call patterns, and alerting security teams when agent behavior deviates from expected boundaries.
MCP Manager by Usercentrics
Best MCP Gateway for Enterprises That Need Purpose-Built MCP Governance
MCP Manager was designed and built for MCP governance. This gateway platform was not adapted from an API gateway, nor was it bolted onto an AI platform or retrofitted from a developer tool. For enterprises where security, compliance, and IT governance are primary requirements, that architectural focus matters. Every feature in MCP Manager exists to answer the questions that enterprise governance teams actually ask.
While many enterprise MCP gateways start at $25,000+ per year, MCP Manager’s pricing is based on the capabilities your organization actually uses, making it viable across a range of enterprise budgets without sacrificing governance depth.
What enterprises get with MCP Manager:
- Private MCP registry with one-click deployment: Maintain an approved catalog of MCP servers and push them across clients like Claude and Cursor organization-wide, without requiring individual developer configuration. MCP Manager also has workflows that make it easy for employees to request approvals on servers.
- RBAC and ABAC: Define access at the user, team, agent and tool level. Attribute-based policies add contextual rules. These rules enable governance that reflects how enterprises actually organize access, not just who has which role.
- Runtime guardrails and MCP-specific threat protection: Automated defense against MCP rug pull attacks and data exfiltration. Real-time monitoring surfaces abnormal patterns before they become incidents.
- PII and sensitive data detection: A Microsoft Presidio integration offers pre-trained PII detection, making it capable of intercepting API keys regulated data before it reaches an LLM. This is a control that compliance frameworks increasingly expect for any system touching customer data.
- Audit logs with full contextual metadata: Every tool call recorded with agent identity, tool name, parameters, result, and the human authorization chain. This is the audit trail that SOC 2, HIPAA, and GDPR auditors require.
- SIEM integration via OpenTelemetry: Export telemetry to your existing security stack — Splunk, Datadog, or whatever your SOC already operates — rather than managing a parallel monitoring system.
- SSO and enterprise IdP integration: Plug into your existing identity infrastructure for consistent authentication across MCP access.
- Org-wide dashboards with real-time alerts: Centralized visibility into all agent activity across every team and business unit, with proactive notifications when behavior deviates from expected patterns.
- Tool and team provisioning: Scope which toolsets each team and agent can access, keeping tool manifests lean and ensuring business units only interact with approved capabilities.
You can try MCP Manager for free after booking an onboarding call. For enterprises evaluating MCP gateways, MCP Manager is the option where governance isn’t a feature — it’s the entire product.
Kong AI Gateway
Best for Enterprises Already Running Kong at Scale
Kong has been a mainstay of enterprise API infrastructure since 2015, and, therefore, many large organizations already route significant API traffic through Kong’s platform. For those enterprises, extending Kong to govern MCP traffic is the consolidation play: same platform, same operational patterns, and same monitoring pipelines.
Kong’s MCP capabilities are substantive. The AI Gateway includes an MCP Proxy plugin for protocol bridging between MCP and HTTP, OAuth 2.1 support through a dedicated MCP OAuth2 plugin, MCP-specific Prometheus metrics, and an MCP Registry in Kong Konnect for centralized tool discovery and governance.
For enterprises with existing Kong infrastructure, the MCP add-on is compelling. MCP governance sits alongside API governance in a familiar platform that security and operations teams already know how to manage.
The downside is that Kong’s MCP features are extensions of a much broader API management platform, and enterprise pricing reflects that scope. Deployments can exceed $50,000 annually, and organizations adopting Kong specifically for MCP are taking on significant platform complexity beyond the MCP use case. Additionally, while Kong’s MCP capabilities are real, they were built by extending API gateway patterns rather than designing specifically for MCP threat models.
Amazon Bedrock AgentCore Gateway
Best for Enterprises Running AI Workloads on AWS
For enterprises where AWS is the infrastructure foundation, AgentCore Gateway integrates MCP governance into the ecosystem IT and security teams already operate. It’s fully managed with no infrastructure to provision or maintain. It also connects natively to IAM for authorization, CloudWatch for monitoring, and CloudTrail for audit logging.
AgentCore Gateway converts existing REST APIs and Lambda functions into MCP-compatible tools without custom code; this can accelerate enterprise rollout significantly. The gateway supports both two-legged and three-legged OAuth through AgentCore Identity, IAM-based authorization with SigV4 signing, and 1-click integrations with tools like Salesforce, Slack, Jira, Asana, and Zendesk.
Two features are particularly relevant for enterprise-scale deployments.
- Semantic tool discovery: as organizations scale to hundreds or thousands of tools, AgentCore Gateway’s built-in search lets agents find the right tool based on intent rather than loading every option into context , which reduces token costs and improving tool selection accuracy.
- Policy integration: AgentCore Policy intercepts every tool call through the gateway, evaluating requests against deterministic Cedar policies before allowing execution. Policies can be authored in natural language and automatically converted to Cedar, making policy creation accessible to security and compliance teams without requiring specialized coding expertise. Every enforcement decision is logged through CloudWatch.
The main point to consider here is commitment and compatability. AgentCore Gateway is a managed service within the broader Bedrock ecosystem, not a standalone gateway. Enterprises that are multi-cloud or need MCP governance that spans beyond AWS boundaries will face integration friction. Organizations evaluating MCP gateways as independent infrastructure will find more portable options elsewhere on this list.
IBM ContextForge
Best for Large Enterprises Needing Federated MCP Governance Across Business Units
ContextForge is IBM’s open-source AI gateway, designed for the architectural complexity that large enterprises face: multiple teams, multiple deployment environments, and governance requirements that vary across business units and geographies.
What distinguishes ContextForge from other options is its multi-protocol federation. It doesn’t just handle MCP. Instead, it federates MCP servers, A2A (Agent-to-Agent) protocol agents, and REST/gRPC APIs into a single unified endpoint with centralized governance. For enterprises running heterogeneous AI architectures where different teams use different protocols, ContextForge provides one control plane across all of them.
Key capabilities for enterprise deployments:
- Multi-cluster federation: Redis-backed federation enables multiple ContextForge instances to interoperate across organizational boundaries, regions, or security domains — each maintaining independent governance while sharing tool discovery.
- Broad SSO integration: Supports GitHub, Google, Microsoft Entra, Okta, Keycloak, IBM Security Verify, and generic OIDC, which covers the identity providers most enterprises already operate.
- RBAC/ABAC with multi-tenancy: Private, team, and global catalogs enable governance structures that mirror how enterprises actually organize teams and access.
- OpenTelemetry observability: Native integration with Phoenix, Jaeger, Zipkin, and other OTLP backends for distributed tracing.
- Admin UI with airgapped deployment support: Manage configuration and monitor activity through a web interface that works in environments without external network access.
ContextForge is deployed via PyPI, Docker, or Helm charts, and scales from single-instance deployments to multi-regional Kubernetes clusters. It also supports multi-databases, such as PostgreSQL, MySQL, and SQLite, making it viable for many different enterprise infrastructure preference.
ContextForge has progressed through beta to release candidates focused on production hardening, including 40+ security controls, Cedar RBAC, mTLS support, and comprehensive testing. However, there is no commercial support. IBM maintains ContextForge as an open-source project, so your team owns operations, troubleshooting, and upgrades entirely. Enterprises with dedicated platform engineering teams comfortable running complex open-source infrastructure will find ContextForge’s capabilities compelling. Organizations that need vendor-backed SLAs or production support should weigh that operational responsibility carefully.
Obot
Best for Enterprises That Require Open-Source Infrastructure With Full Data Sovereignty
Some enterprises can’t route AI agent traffic through third-party infrastructure. Whether driven by data residency regulations, internal security policies, or procurement requirements that favor open-source, these organizations need MCP governance they can run entirely within their own environment.
Obot is an open-source MCP platform that provides server hosting, a searchable registry of approved tools, a gateway routing layer, and a built-in chat client. This is all deployable on your own Kubernetes infrastructure. IT maintains full control over where data flows, what’s logged, and who has access.
The curated MCP catalog is particularly valuable at enterprise scale. Instead of every team discovering and deploying their own MCP servers from the open-source ecosystem (many of which have quality or security problems) IT can maintain an approved registry of vetted servers. Employees browse the catalog, connect to approved tools, and authenticate through the enterprise IdP. The open-source edition supports GitHub and Google for identity; the Enterprise Edition adds Okta and Microsoft Entra for organizations that require those integrations.
The gateway proxies all MCP traffic, while a shim alongside each server handles authorization, audit logging, and OAuth token exchange. Credentials and secrets live in the shim and are never exposed to the MCP server itself, which limits the blast radius of a compromised server.
The potential diwnload is that self-hosting means your team owns the full operational lifecycle: deployment, scaling, patching, monitoring, and incident response. For enterprises with platform engineering capacity, that’s the point though, as you get total control. For enterprises without Kubernetes expertise on staff, the operational commitment may be a more significant undertaking than adopting a managed solution.
Choosing the Right MCP Gateway for Your Enterprise
The right gateway depends on your existing infrastructure, your compliance posture, and how much operational ownership you’re prepared to take on.
- If MCP governance is the primary requirement: MCP Manager by Usercentrics was built for this use case from the ground up. This option is best if you want RBAC, ABAC, PII detection, SIEM integration, immutable audit logs, and runtime threat protection all in a single platform priced for the capabilities you actually use. You can learn more about MCP Manager and book a free trial.
- If you already run Kong for API management: Extending Kong to include MCP governance consolidates tooling into a platform your team already operates, though the pricing and platform scope exceed what MCP alone requires.
- If your infrastructure runs on AWS: AgentCore Gateway integrates natively with IAM, CloudWatch, CloudTrail, and Cedar-based policy enforcement. The commitment to the Bedrock ecosystem is the key consideration.
- If you need federated governance across multiple business units and protocols: IBM ContextForge provides multi-cluster federation, multi-protocol support (MCP, A2A, REST/gRPC), and the architectural flexibility that large, complex enterprises require — with the tradeoff of beta-stage software and no commercial support.
- If data sovereignty and open-source infrastructure are non-negotiable: Obot gives you a complete MCP platform you can run entirely within your own environment, with full control over data, access, and operations.
Every enterprise will eventually need an MCP gateway. The agents are already deployed, the data is already flowing, and the compliance clock is already ticking. The question isn’t whether to add a governance layer. If you do, you can try MCP Manager for free to see how it works or learn more in the webinar below.